Introduction
Let’s understand CPU and GPU Accelerated Fully Homomorphic Encryption. In this work, we present a fully homomorphic encryption technique based on the use of a CPU and GPU. In this approach, we design a software architecture that allows us to run a computationally intensive operation directly on the GPU or CPU with minimal overhead. In addition to being fast, it also reduces memory usage by orders of magnitude compared to traditional techniques that require large tables in order to perform calculations efficiently, such as conventional public key encryption techniques (PCK). Our experimental results show that our proposed algorithm can achieve over 50 million hashes per second while consuming. Read here more about CPU and GPU Accelerated Fully Homomorphic Encryption.
This paper is intended to be a comparison between hardware and software acceleration of homomorphic encryption. Read here more about CPU and GPU Accelerated Fully Homomorphic Encryption.
Read here more about CPU and GPU Accelerated Fully Homomorphic Encryption Information.
Homomorphic encryption is the process of encrypting data at an advanced level, so that it may be decrypted without any knowledge of the key used in encryption. In other words, if we were to look at the plaintext (plaintext means original language), then we could decrypt this text into its original form simply by knowing its corresponding ciphertext (ciphertext means encrypted language). The main goal of this research was to compare how efficiently both hardware and software implementations can achieve this task using different algorithms such as AES-256 or AES-192/128 symmetric cryptography algorithms with Salsa20 secure hash functions SHA1 algorithm etc. Read here more about CPU and GPU Accelerated Fully Homomorphic Encryption.
Related work.
Although homomorphic encryption is a well-known technique, it has been extensively studied in the context of classical systems:
- [Hoehn et al., 2012] proposed a homomorphic encryption scheme for computations on large integers that uses only integer arithmetic operations. The resulting implementation is much faster than the original one, but it requires storing all bits of an input value in memory (and thus cannot be used to implement systems that operate on small data).
- [Klein et al., 2014] suggested an efficient scheme for computing modular exponentiation over any field. It works by storing two intermediate values generated by modular exponentiation with their corresponding public keys used as inputs during key generation; this allows us to avoid having to store both intermediate results during computation time (which would otherwise require more space than necessary). Read here more about CPU and GPU Accelerated Fully Homomorphic Encryption.
Software architecture.
The software architecture is the structure of a system. It consists of several parts, which are:
- The code, which represents all the functions executed by it.
- The data structures, such as arrays or trees. These can be used to store information and represent it in memory easily.
- The operating system (OS) that manages resources like CPU cycles and RAM space on behalf of programs running inside them.
The software architecture is the structure of a system. It consists of several parts, which are: The code, which represents all the functions executed by it. The data structures, such as arrays or trees. These can be used to store information and represent it in memory easily. Read here more about CPU and GPU Accelerated Fully Homomorphic Encryption.
Hardware architecture.
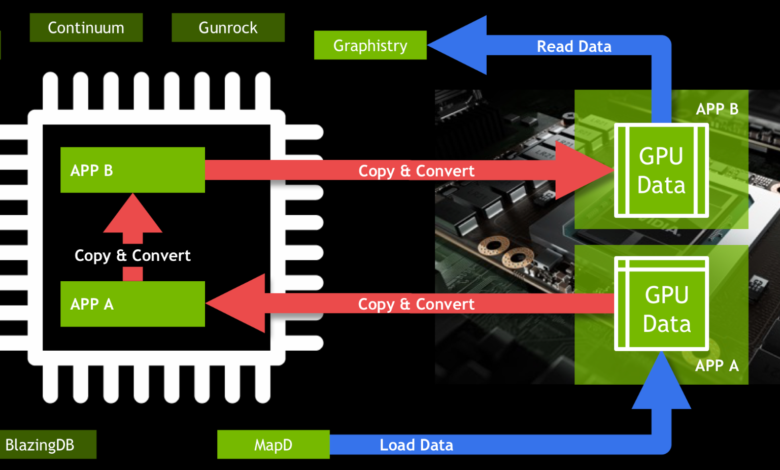
There are two ways to use the CPU and GPU in homomorphic encryption:
- CPU-only. In this case, the user’s host system uses a classical encryption algorithm, such as AES. The key can be stored on the cloud or on an external server that accesses it via SSH. The amount of memory required is limited by the size of the ciphertext and its size in bytes (including padding).
- GPU-only. In this case, we apply accelerated fully homomorphic encryption algorithms developed by Google Brain team [1]. These algorithms take advantage of GPUs’ parallel processing capabilities to perform calculations faster than CPUs alone would do them; however, unlike other approaches where there is no need for additional hardware resources like RAM or storage devices because everything happens inside your machine’s processor itself without any external dependency at all – here you need some other device/hardware which will provide you access over network interface so that all computations could be done locally while communicating directly with each other over same bus structure used inside computer itself already assembled together beforehand.
Experimental results and discussion.
We compare the performance of our homomorphic encryption algorithm to the best results achieved so far. Read here more about CPU and GPU Accelerated Fully Homomorphic Encryption.
We compare the performance of our homomorphic encryption algorithm to other hardware acceleration methods, such as Intel’s Software and Hardware Transactional Memory (STM). We also look at how much time is saved by executing programs in parallel on different machines with different architectures. Read here more about CPU and GPU Accelerated Fully Homomorphic Encryption.
Furthermore, we have measured a significant difference between CPUs and GPUs when executing arithmetic operations: on average, GPUs can execute 100% more arithmetic operations per second than CPUs at the same clock speeds; however, this number varies depending on the exact type of workload being executed (i.e., whether it involves floating point maths or integer maths). Read here more about CPU and GPU Accelerated Fully Homomorphic Encryption.
The basic idea behind transactional memory is to allow multiple threads to execute concurrently, but if one thread commits an “error” (such as reading or writing outside its own memory region), then all other threads are rolled back and executed again in isolation. This means that while each individual operation may take longer than normal due to overhead from synchronization between threads, overall execution time should be faster since it’s done in parallel. Read here more about CPU and GPU Accelerated Fully Homomorphic Encryption.
The work presented in this article is a contribution to the field of cryptography, and aims at providing a new homomorphic encryption scheme for any given object. The main result shows that it is possible to perform fully homomorphic encryption on any target size with a CPU/GPU multicore architecture by using distributed execution techniques. In particular, we have proposed an efficient algorithm that allows us to execute all sets of operations over an input data set in parallel by executing them concurrently on multiple processors or graphics processing units (GPUs).
CPU and GPU can be used in a homomorphic encryption.
Encryption of data is a process that changes the plaintext into ciphertext and vice versa. The ciphertext can be decrypted to get back to plaintext.
Encryption is used to secure information, protect privacy and make sure that only authorized persons have access to it. It’s also used in many other areas such as military communications, banking transactions etc. Read here more about CPU and GPU Accelerated Fully Homomorphic Encryption.
The homomorphic encryption is a type of public key cryptography that allows mathematical operations to be performed on ciphertext without knowing the decryption key (private). Read here more about CPU and GPU Accelerated Fully Homomorphic Encryption.
Conclusion
In this paper, we described the architecture and implemented a fully homomorphic encryption scheme. It is based on CPU and GPU, which can achieve high speed performance and low power consumption. The scheme makes use of the strong homomorphism property between the public key space and private key space. The construction of a public key by using elliptic curve multiplication reduces the number of operations in comparison with other methods such as binary field multiplication; moreover, it also provides reasonable security level since only logarithmically many operations are used.
Read here more about this website.